Explain why an organization's firewall should block outgoing packets the source addresses of which are not in the organization's address space.
Answers
Answer:
A firewall is used to monitor and control incoming and outgoing (or in better terms, inbound and outbound) traffic in a network based on some pre-defined security rules set by either an individual or a business.
Now, using firewall to block outgoing packets that have source addresses which are not in an organization's address space means rejecting requests that, though originate from the organization's address space, are not in the organization's allowable address.
This is necessary and of utmost importance because even though an hacker (or simply an attacker) gains access into the organization's network, there is a limit to what harm they can do. If for example, they manage to get some malicious programs into the system's via network processes such as using infected e-mails or using a browser, they might also want to make some requests to the Internet to get some additional programs downloaded which altogether is harmful to the system. Disabling or blocking outgoing packets or traffic will stop this combined hazard from happening.
Related Questions
Select all the correct answers.
Which two tasks are responsibilities of a network administrator?
setting up an internet connection for a network
designing a network
repairing faulty routers
ensuring there are no conflicting IP addresses on the network
maintaining a network
A malicious user launches an attack on a private network and believes the attack has been successful. However the target network is not compromised. What security measure is it most likely using?
A. Only a firewall
B. A demilitarized zone with a firewall
C. Network segmentation
D. A virtual private network
I also put a picture of another question. Help me fast bc the test is timed.

Answers
Explanation:
I hope this helps ;}
BTW PLATO

The purpose of validating the results of the program is Group of answer choices To create a model of the program To determine if the program solves the original problem To correct syntax errors To correct runtime errors
Answers
Answer:
To determine if the program solves the original problem
Explanation:
Required
Essence of validating a program
From list of given options, only the above option best describes the given illustration.
When a program is validated, it means that the results of the program are tested to meet the requirements of the user;
For a program to be validated, it means it has passed the stage of error checking and correction; whether syntax or run time errors;
However, when modifications are made, the program will need to be re-validated to ensure that it comports with its requirements.
Why is wind power a never ending source of power?
Answers
Answer:
"Wind is caused by the heating of the atmosphere which is caused by the sun. Since we have the sun we have wind, since we will never lose the sun, we will never lose the wind which means it is a never-ending source of power." It's also the reason why wind power is a form of solar energy, along with that wind power does not contribute to the heating of the Earth's surface like burning fossil fuels. Very healthy for the environment of the planet.
Hope this helps.
A _____ is a smaller image of a slide.
template
toolbar
thumbnail
pane
Answers
What additional uses of technology can u see in the workplace
Answers
Answer:
Here are some additional uses of technology in the workplace:
Virtual reality (VR) and augmented reality (AR) can be used for training, simulation, and collaboration. For example, VR can be used to train employees on how to operate machinery or to simulate a customer service interaction. AR can be used to provide employees with real-time information or to collaborate with colleagues on a project.Artificial intelligence (AI) can be used for a variety of tasks, such as customer service, data analysis, and fraud detection. For example, AI can be used to answer customer questions, identify trends in data, or detect fraudulent activity.Machine learning can be used to improve the accuracy of predictions and decisions. For example, machine learning can be used to predict customer churn, optimize marketing campaigns, or improve product recommendations.Blockchain can be used to create secure and transparent records of transactions. For example, blockchain can be used to track the provenance of goods, to manage supply chains, or to record financial transactions.The Internet of Things (IoT) can be used to connect devices and collect data. For example, IoT can be used to monitor equipment, track assets, or collect data about customer behavior.These are just a few of the many ways that technology can be used in the workplace. As technology continues to evolve, we can expect to see even more innovative and creative uses of technology in the workplace.
working with the tkinter(python) library
make the window you create always appear on top of other windows. You can do this with lift() or root.attributes('-topmost', ...), but this does not apply to full-screen windows. What can i do?
Answers
To make a tkinter window always appear on top of other windows, including full-screen windows, you must use the wm_attributes method with the topmost attribute set to True.
How can I make a tkinter window always appear on top of other windows?By using the wm_attributes method in tkinter and setting the topmost attribute to True, you can ensure that your tkinter window stays on top of other windows, even when they are in full-screen mode.
This attribute allows you to maintain the window's visibility and prominence regardless of the current state of other windows on your screen.
Read more about python
brainly.com/question/26497128
#SPJ1
What is the purpose of a poster frame?
to allow the contents of an embed code to be displayed
to insert a downloaded video for offline playback and editing
to create the frame in which a screen recording will be inserted
to capture a portion of a video clip to show as a preview image
Answers
Answer: the last one
Explanation:
Here is the answer::

Someone please solve this

Answers
Answer:
126=01111110
Explanation:
To solve this you simply have to get the sum of all your numbers to be equal to the number on the left using the biggest numbers possible
For 126,
First you look at 128, since 128>126 we can't use this and leave it as 0
126>64 so we put that as 1
We then subtract this 64 from 126 and get 62
Since 62>32 we put 32 as 1 and subtract 32 from 62
Then we see that 30>16 and put 16 as 1 and subtract 16 from 30
Now we have 14, since 14>8 we put 8 as 1 and subtract 8 from 14
Now we have 6, since 6>4 we put 4 as 1 and subtract 4 from 6
Lastly we have 2==2, since 2 can go into 2 we would put 2 as 1 and then subtract 2 from 2
Now we have 0 left and don't have to do anything with 1, so we leave it as 0
When you put it all together, you get 01111110
Database queries is an example of
Answers
Answer:
A query in a database is a request for information stored within a database management system (DBMS), which is the software program that maintains data.
SQL(Structured Query Language ( is a standard language for storing, manipulating, and retrieving data in database.
Five types of SQL queries are:
1) Data Definition Language (DDL).
used to define and modify the structure of a database.
2) Data Manipulation Language (DML).
used to manipulate (change) the data in the database.
3) Data Control Language(DCL).
used for access control and permission management for users in the database.
4) Transaction Control Language(TCL).
used for maintaining consistency of the database and for the management of transactions made by the DML commands.
5) Data Query Language (DQL).
used for performing queries on the data within schema objects.
1. Fill in the blanks with appropriate word. 5°1-5 is a collection of raw unprocessed facts, figures, and symbols
Answers
Answer:
e
Explanation:
e
Where are options to add a border around the outside of a chart found?
Answers
Answer:
on the tool bar, there is an icon that looks like a window.
Explanation:
Answer:
B. Format tab in the Shape Styles group
Explanation:
EDGE 2020 gang gang
xamine the following output:
Reply from 64.78.193.84: bytes=32 time=86ms TTL=115
Reply from 64.78.193.84: bytes=32 time=43ms TTL=115
Reply from 64.78.193.84: bytes=32 time=44ms TTL=115
Reply from 64.78.193.84: bytes=32 time=47ms TTL=115
Reply from 64.78.193.84: bytes=32 time=44ms TTL=115
Reply from 64.78.193.84: bytes=32 time=44ms TTL=115
Reply from 64.78.193.84: bytes=32 time=73ms TTL=115
Reply from 64.78.193.84: bytes=32 time=46ms TTL=115
Which of the following utilities produced this output?
Answers
The output provided appears to be from the "ping" utility.
How is this so?Ping is a network diagnostic tool used to test the connectivity between two network devices,typically using the Internet Control Message Protocol (ICMP).
In this case, the output shows the successful replies received from the IP address 64.78.193.84,along with the response time and time-to-live (TTL) value.
Ping is commonly used to troubleshoot network connectivity issues and measureround-trip times to a specific destination.
Learn more about utilities at:
https://brainly.com/question/30049978
#SPJ1
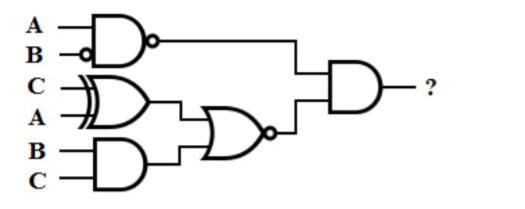
Can someone help me with the following logical circuit, perform two actions. FIRST, convert the circuit into a logical
statement. SECOND, create a truth table based on the circuit/statement. (20 pts. each for statement and
truth table.
Answers
Creation of Truth Table Based on the logical statement, we can create a truth table as shown below:
A B (not A) (not A) and B (not A) and B or A A or (not A) and B 0 0 1 0 1 0 0 1 0 0 1 0 1 1 0 1 1 0 1 1 1 0 1 1 0 1 1 0 1 1 1
The first two columns show the input values, the next column shows the output of the NOT gate, then the output of the AND gate, then the output of the OR gate and finally the output of the logical statement.
We can observe that the output of the logical statement is the same as the output of the OR gate.
Given the logical circuit, we are required to perform two actions on it. Firstly, convert the circuit into a logical statement. Secondly, create a truth table based on the circuit/statement. Let's understand how to do these actions one by one:Conversion of Circuit into Logical Statement.
The given circuit contains three components: NOT gate, AND gate and OR gate. Let's analyze the working of this circuit. The two input variables A and B are first passed through the NOT gate, which gives the opposite of the input signal.
Then the NOT gate output is passed through the AND gate along with the input variable B. The output of the AND gate is then passed through the OR gate along with the input variable A.We can create a logical statement based on this working as: (not A) and B or A. This can also be represented as A or (not A) and B. Either of these statements is correct and can be used to construct the truth table.
Creation of Truth Table Based on the logical statement, we can create a truth table as shown below:
A B (not A) (not A) and B (not A) and B or A A or (not A) and B 0 0 1 0 1 0 0 1 0 0 1 0 1 1 0 1 1 0 1 1 1 0 1 1 0 1 1 0 1 1 1
In the truth table, we have all possible combinations of input variables A and B and their corresponding outputs for each component of the circuit.
The first two columns show the input values, the next column shows the output of the NOT gate, then the output of the AND gate, then the output of the OR gate and finally the output of the logical statement.
We can observe that the output of the logical statement is the same as the output of the OR gate.
For more such questions on Truth Table, click on:
https://brainly.com/question/13425324
#SPJ8
Your company has been assigned the 194.10.0.0/24 network for use at one of its sites. You need to calculate a subnet mask that will accommodate 60 hosts per subnet while maximizing the number of available subnets. What subnet mask will you use in CIDR notation?
Answers
To accommodate 60 hosts per subnet while maximizing the number of available subnets, we need to use a subnet mask that provides enough host bits and subnet bits.
How to calculateTo calculate the subnet mask, we determine the number of host bits required to accommodate 60 hosts: 2^6 = 64. Therefore, we need 6 host bits.
Subsequently, we determine the optimal quantity of subnet bits needed to increase the quantity of accessible subnets: the formula 2^n >= the amount of subnets is used. To account for multiple subnets, the value of n is set to 2, resulting in a total of 4 subnets.
Therefore, we need 2 subnet bits.
Combining the host bits (6) and subnet bits (2), we get a subnet mask of /28 in CIDR notation.
Read more about subnet mask here:
https://brainly.com/question/28390252
#SPJ1
in python Simple geometry can compute the height of an object from the object's shadow length and shadow angle using the formula: tan(angleElevation) = treeHeight / shadowLength. Given the shadow length and angle of elevation, compute the tree height.
Sample output with inputs: 0.4 17.5
Tree height: 7.398881327917831
Answers
Answer:
import math
angle = float(input('Enter Angle: '))
shadowLength = float5(input('Enter Shadow Length: '))
tree_height = math.tan(angle)*shadowLength
print('Tree Height = {}'.format(tree_height))
Explanation:
From the equation given, the first step is to derive the equation for calculating the Tree Height.
In order to calculate the tangent of an angle, the math module has to be imported. math module allows the program to perform advanced math operations.
The program then prompts the user to input values for angle and shadow length.
The inputted values are converted to floats and used in the equation that was derived for Tree height.
Three height is evaluated and the result is printed to the screen

importance of sorting elements in data structure
Answers
Answer:
The arrangement of data in a preferred order is called sorting in the data structure. By sorting data, it is easier to search through it quickly and easily. The simplest example of sorting is a dictionary.
Explanation:
How do you modify WordArt? Give specific details and steps
NEED THIS ASAP
Answers
The steps to modify a WordArt text are:
Click on the Editing WordArt TextThen Double click or select the WordArt image.Via the use of the Format command tab, in the Text group, select Edit Text and the Edit WordArt Text dialog box showThrough the use of the Text text box, make all changes you want.Select OK.What is Word art?Word art or text art is known to be a kind of an art that is made up of text, creating words or phrases along with visual imagery.
Therefore, The steps to modify a WordArt text are:
Click on the Editing WordArt TextThen Double click or select the WordArt image.Via the use of the Format command tab, in the Text group, select Edit Text and the Edit WordArt Text dialog box showThrough the use of the Text text box, make all changes you want.Select OK.
Learn more about WordArt from
https://brainly.com/question/938171
#SPJ1
What does the office background allow you to do?
Answers
Answer: Any changes that you make to the Office Background in PowerPoint 365 will be reflected in all other Microsoft Office 365 products on your computer, such as Word, Excel, Outlook, and others. These patterned strips are not activated by default.
Snippet 1: check_file_permissions.c #include
1
#include
#include
int main (int argc, char* argv[])
{ char* filepath = argv[1];
int returnval;
// Check file existence returnval = access (filepath, F_OK);
if (returnval == 0) printf ("\n %s exists\n", filepath);
else { if (errno == ENOENT) printf ("%s does not exist\n", filepath);
else if (errno == EACCES) printf ("%s is not accessible\n", filepath);
return 0; }
// Check read access ...
// Check write access ...
return 0;
}
0.
(a) Extend code snippet 1 to check for read and write access permissions of a given file
(b) Write a C program where open system call creates a new file (say, destination.txt) and then opens it. (Hint: use the bitwise OR flag)
1. UNIX cat command has three functions with regard to text files: displaying them, combining copies of them and creating new ones.
Write a C program to implement a command called displaycontent that takes a (text) file name as argument and display its contents. Report an appropriate message if the file does not exist or can’t be opened (i.e. the file doesn’t have read permission). You are to use open(), read(), write() and close() system calls.
NOTE: Name your executable file as displaycontent and execute your program as ./displaycontent file_name
2. The cp command copies the source file specified by the SourceFile parameter to the destination file specified by the DestinationFile parameter.
Write a C program that mimics the cp command using open() system call to open source.txt file in read-only mode and copy the contents of it to destination.txt using read() and write() system calls.
3. Repeat part 2 (by writing a new C program) as per the following procedure:
(a) Read the next 100 characters from source.txt, and among characters read, replace each character ’1’ with character ’A’ and all characters are then written in destination.txt
(b) Write characters "XYZ" into file destination.txt
(c) Repeat the previous steps until the end of file source.txt. The last read step may not have 100 characters.
Answers
Answer:
I don't know you should figure that out good luck
Explanation:
good luck
What does NOT match with Agile Manifesto?
Select the correct option(s) and click Submit.
Processes and tools over individuals and interactions
Working software over comprehensive documentation
Responding to change over following a plan
ent...
ed!
e Ai...
Contract negotiation over customer collaboration
Answers
Answer:
yes
Explanation:
List the five component of information system
Answers
Answer:
hardware, software, database, network and people
Which sentence best descibes an activity stream
Answers
Answer: a list of recent activities performed by an individual, typically on a single website.
Explanation:
What kind of variable is measured using 2 different values
Answers
A variable that is measured using two different values can be classified as a categorical variable or a binary variable.
Depending on the nature of the values, a variable can be classified as:
1)Categorical Variable: If the two different values represent distinct categories or groups, the variable is considered categorical. In this case, the variable can take on only one of two possible values.
Examples include gender (male/female), presence/absence of a certain trait, yes/no responses, or any other classification with mutually exclusive categories.
2)Binary Variable: If the two different values represent two distinct outcomes or states, the variable can be classified as a binary variable. Binary variables are often used in statistics, machine learning, and hypothesis testing.
Examples include success/failure, true/false, 1/0, or positive/negative results.
It's important to note that the distinction between categorical and binary variables lies in the nature of the values and the underlying meaning they convey.
Categorical variables can have more than two categories, while binary variables specifically refer to variables with only two possible values.
For more questions on variable
https://brainly.com/question/28248724
#SPJ8
first box options: Forums, Emails, Chats
second box options: Message boards, Chats, Blogs
third box options: Forums, Blogs, Websites

Answers
Answer:
the first box is chats, the second box is message, and the third box is websites
Explanation:
The reason the first box is chats is because chats are able to let you receive and send messages. The reason the second box is messages is because when you message someone your having a conversation online. and the reason The third box is Websites is because online you can publish articles or journal entries therefore making the first box chats, the second box message, and the third box website. Hope this helps
Taking on a programming internship does not provide training and is of little value to an intern. True or False.
Answers
Answer:
the correct answer is False
Read a number, add 10% and output the result.
Answers
Let's use python
Program:-
\(\tt num=(int(input("Enter\:the\: number:")))\)
\(\tt p=0.1*num\)
\(\tt print("The\: result\:is",p)\)
Sample output:-
Enter the number: 100
The result is 10
Palindrome.java
Question:
Write an application that determines whether a phrase entered by the user is a palindrome. A palindrome is a phrase that reads the same backward and forward without regarding capitalization or punctuation. For example, “Dot saw I was Tod”, “Was it a car or a cat I saw”, and “Madam Im Adam” are palindromes. Display the appropriate feedback: You entered a palindrome or You did not enter a palindrome.
CODE:
import java.util.*;
public class Palindrome {
public static void main(String[] args) {
Scanner sc = new Scanner(System.in);
System.out.println("Enter phrase : ");
String phrase = sc.nextLine();
phrase = phrase.replace(" ", "").toLowerCase();
phrase = phrase.replaceAll("[^a-zA-Z0-9]", "");
int i = 0, j = phrase.length() - 1;
boolean ispalindrome= true;
while (i < j) {
if (phrase.charAt(i) != phrase.charAt(j)) {
ispalindrome = false;
}
i++;
j--;
}
if(ispalindrome)
{
System.out.println("you entered a palindrome.");
}
else
{
System.out.println("you did not enter a palindrome.");
}
}
}
RESULTS:
50% good
pls help
Answers
1) If a robot has a 3 bit instruction set and needs 20 instructions to reach its destination, how many bits of memory are required?
2) A robot driven by a raspberry Pi has 256MB of memory. The robot has a 3 bit instruction set. What is the maximum number of instructions that can be loaded into the robot?
3) Imagine that the robot with 256MB of memory needs 500,000 4-bit instructions to perform a job. Would it be possible to load in all the 500,000 instructions into the memory of the robot?
Answers
Answer:
Explanat500,000ion:
Compare and contrast predictive analytics with prescriptive and descriptive analytics. Use examples.
Answers
Explanation:
Predictive, prescriptive, and descriptive analytics are three key approaches to data analysis that help organizations make data-driven decisions. Each serves a different purpose in transforming raw data into actionable insights.
1. Descriptive Analytics:
Descriptive analytics aims to summarize and interpret historical data to understand past events, trends, or behaviors. It involves the use of basic data aggregation and mining techniques like mean, median, mode, frequency distribution, and data visualization tools such as pie charts, bar graphs, and heatmaps. The primary goal is to condense large datasets into comprehensible information.
Example: A retail company analyzing its sales data from the previous year to identify seasonal trends, top-selling products, and customer preferences. This analysis helps them understand the past performance of the business and guide future planning.
2. Predictive Analytics:
Predictive analytics focuses on using historical data to forecast future events, trends, or outcomes. It leverages machine learning algorithms, statistical modeling, and data mining techniques to identify patterns and correlations that might not be evident to humans. The objective is to estimate the probability of future occurrences based on past data.
Example: A bank using predictive analytics to assess the creditworthiness of customers applying for loans. It evaluates the applicants' past financial data, such as credit history, income, and debt-to-income ratio, to predict the likelihood of loan repayment or default.
3. Prescriptive Analytics:
Prescriptive analytics goes a step further by suggesting optimal actions or decisions to address the potential future events identified by predictive analytics. It integrates optimization techniques, simulation models, and decision theory to help organizations make better decisions in complex situations.
Example: A logistics company using prescriptive analytics to optimize route planning for its delivery truck fleet. Based on factors such as traffic patterns, weather conditions, and delivery deadlines, the algorithm recommends the best routes to minimize fuel consumption, time, and cost.
In summary, descriptive analytics helps organizations understand past events, predictive analytics forecasts the likelihood of future events, and prescriptive analytics suggests optimal actions to take based on these predictions. While descriptive analytics forms the foundation for understanding data, predictive and prescriptive analytics enable organizations to make proactive, data-driven decisions to optimize their operations and reach their goals.
The user can set their own computer hostname and username. Which stage of the hardware lifecycle does this scenario belong to?
Answers
Answer:
Deployment
Explanation:
Hardware lifecycle management is geared at making optimum use of the computer hardware so as to maximize all the possible benefits. During the deployment stage of the hardware lifecycle, the user is prompted by the computer to input their own computer hostname and username. In doing this, it is important that the user takes note of possible flaws in security. Passwords are set at this stage too. The four stages in the hardware lifecycle are procurement, deployment, maintenance, and retirement. At the deployment stage, the hardware is set up and allocated to employees so that they can discharge their duties effectively.
So, for organizations, it is important that strong passwords are used to prevent security breaches in the event that an employee leaves the organization.
Answer:
Deployment
Explanation: