you need to implement a symbol table. the goal is to optimize the performance (maximize the speed) of an average look-up. which data structure should you use for your symbol table?
Answers
The most popular way to build symbol tables is by maintaining two tables, a hash table and a symbol table, which is known as a hashing scheme.
How should a symbol table be implemented? What data format is best?The most popular way to build symbol tables is by maintaining two tables, a hash table and a symbol table, which is known as a hashing scheme. An array containing a hash table has an index range of 0 to table size – 1. Pointers pointing to the names of the symbol table are contained in these entries.You can use one of the following methods to implement a symbol table a linear (sorted or unsorted) list, a binary search tree, and a hash table.You can use one of the following methods to implement a symbol table is a linear list, either sorted or unsorted, a hash table, Binarized search tree.To learn more about Hashing scheme refer to:
https://brainly.com/question/23531594
#SPJ4
Related Questions
Which laptop has the larger non volatile storage capacity
Answers
1. MacBook Pro (16-inch): This laptop offers storage options ranging from 512GB to 8TB.
2. Dell XPS 15: This laptop offers storage options ranging from 256GB to 2TB.
3. HP Spectre x360: This laptop offers storage options ranging from 256GB to 2TB.
4. ASUS ROG Zephyrus G14: This laptop offers storage options ranging from 512GB to 1TB.
5. Acer Aspire 5: This laptop offers storage options ranging from 256GB to 1TB.
It is important to note that the storage capacity of a laptop depends on the model and can vary.
the amount of movement you can make in a joint is called your . 2. exercises including jumping, skipping, and calisthenics (such as those used in a warm-up) are called exercises.
Answers
The amount of movement you can make in a joint is called your range of motion. Range of motion refers to the degree to which a joint can move in different directions. It is determined by the flexibility of the muscles, tendons, and ligaments surrounding the joint.
Exercises including jumping, skipping, and calisthenics (such as those used in a warm-up) are called dynamic exercises. Dynamic exercises involve continuous movement of the body and are typically used to improve cardiovascular fitness, strength, and flexibility.
These exercises are characterized by their ability to engage multiple muscle groups and elevate heart rate. Dynamic exercises are often used in warm-up routines to prepare the body for more intense physical activity.
To know more about movement visit:
https://brainly.com/question/11223271
#SPJ11
Mr. reams mixes 12 cups of paint in a large bowl. he uses the paint to fill 40 small dishes with 2 fluid ounces of paint each. how many cups of paint does mr. reams have left in the bowl? hint: there are 8 fluid ounces in 1 cup. cups
Answers
After filling 40 small dishes with 2 fluid ounces of paint each using 12 cups of paint initially, Mr. Reams is left with 2 cups of paint in the bowl.
The given problem involves calculating the amount of paint left in the bowl after Mr. Reams fills 40 small dishes with 2 fluid ounces of paint each, using 12 cups of paint initially. We know that 8 fluid ounces are equal to 1 cup of paint. Therefore, 2 fluid ounces of paint are equal to 2/8 or 1/4 cup of paint. Since Mr. Reams fills 40 small dishes with 2 fluid ounces of paint each, he uses a total of 40 * 1/4 = 10 cups of paint. To find the amount of paint left in the bowl, we need to subtract the amount of paint used from the initial amount of paint. Therefore, the amount of paint left in the bowl is 12 - 10 = 2 cups of paint.
To learn more about fluid ounces, visit:
https://brainly.com/question/28818138
#SPJ11
Match the job task to the occupation that would perform it. 1. Research the causes and treatments of diseases physical scientist 2. Investigate the composition of a planet and its atmosphere electrical engineer 3. Design the circuitry for a television life scientist 4. Develop a prototype for an airplane aerospace engineer
Answers
Answer:
1.Physical scientist
2.Life scientist
3.Electrical engineer
4.aerospace engineer
Explanation:
9.4 Code Practice: Your task is to determine whether each item in the array above is divisible
by 3 or not. If an item is divisible by 3, then leave that value as-is in the
array, but if it is not divisible by 3, then replace that value in the array with a
o. Remember that you will need to use modular division from Unit 2 to
determine if a value is divisible by 3. Finally, print out the array in the
format as seen in the sample run below.
(Can someone please help me?)
Answers
Answer:
Explanation:
The following Python code is a function that takes in an array as a parameter, it then loops through the array determining if the element is divisible by 3. If it is it leaves it alone, otherwise it changes it to a 0. Then ouputs the array. A test case is shown in the attached image below using a sample array.
def divisible_by_three(array):
for x in array:
if x % 3 == 0:
pass
else:
array[array.index(x)] = 0
return array

In this exercise we have to use the knowledge of computational language in python to describe the code, like this:
We can find the code in the attached image.
What is an array for?After wondering what an array is, you might wonder what it's for. The main purpose is to store information in an orderly way, that is, for each line, one piece of information. An example of an array is when storing names of people present in a classroom.
The code can be written more simply as:
def divisible_by_three(array):
for x in array:
if x % 3 == 0:
pass
else:
array[array.index(x)] = 0
return array
See more about python at brainly.com/question/26104476

HELP HELP. I NEED 2 CODES SOLVED


Answers
The code is written in an incorrect syntax and has a few errors. It seems to be a mixture of two different procedures that are not well-defined.
How to explain the codeHowever, based on the structure and assumptions, I can infer that the output of this code will display the value of ans, which is the sum of the result of F(11,20) and G(-4,3).
The result of F(11,20) will be either 20.5 or 20, depending on the value of the variable p in the if-else statement. The result of G(-4,3) will be 3 because the loop inside the G procedure iterates three times, incrementing the value of val by 1 each time, and then returns val, which is 3. Therefore, the output of the code will be 23.
Learn more about code on
https://brainly.com/question/26134656
#SPJ1
Stella has captured this candid photograph of a man who was reunited with his son. She has used facial retouching in each of the images. Which images could she print along with the mans interview?

Answers
Answer: The last picture it looks better.
Explanation: Welcome!
Answer:
4
Explanation:
The EMPLOYEES table contains these columns:
EMPLOYEE_ID NUMBER(9)
LAST_NAME VARCHAR2 (25)
FIRST_NAME VARCHAR2 (25)
SALARY NUMBER(6)
You need to create a report to display the salaries of all employees. Which SQL Statement should you use to display the salaries in format: "$45,000.00"?
Mark for Review
(1) Points
SELECT TO_NUM(salary, '$999,999.00')
FROM employees;
SELECT TO_CHAR(salary, '$999,999')
FROM employees;
SELECT TO_NUM(salary, '$999,990.99')
FROM employees;
SELECT TO_CHAR(salary, '$999,999.00')
FROM employees;
(*)
Answers
The SQL statement that should be used to display the salaries of all employees in the format "$45,000.00" is SELECT TO_CHAR(salary, '$999,999.00') FROM employees;. This statement uses the TO_CHAR function to convert the salary column to a character string with the specified format of "$999,999.00".
The TO_CHAR function in Oracle SQL is used to convert a value of any data type to a string with a specified format. The format model parameter in the function specifies the format in which the value should be displayed. In the given scenario, the TO_CHAR function is used to convert the numeric values in the salary column to a character string with the format '$999,999.00'. The dollar sign $ indicates the currency symbol, and the format 999,999.00 specifies that the value should be displayed with commas separating thousands and two decimal places.
Learn more about function here:
https://brainly.com/question/30395140
#SPJ11
5.What is returned by the call go(30)?
public static String go ( int x)
{
String s = "";
for (int n = x; n > 0; n = n - 5)
S = S + x +
return s;}
Answers
Answer:
The string returned is: 303030303030
Explanation:
Given
The above method
Required
The returned string
The method returns a string that is repeated x/5 times.
Take for instance;
x = 30
The method will return a string that contains x in 30/5 (i.e. 6) times
Hence, the result of go(30) is 303030303030
Please answer these questions thank you

Answers
1. Computers are often used because they are able to hold lots of data in a very small space. They can work quickly and are much better at completing many tasks because of their speed and efficiency.
2. The action processing of data produces information that can be displayed or stored for future use.
3. Two internal components that are necessary for the computer to function are the CPU
(Central Processing Unit) and the RAM (Random Access Memory).
4. The external components of a computer are known as peripherals.
5. Components: CPU, RAM, Motherboard Peripherals: Keyboard, Mouse, Printers, Speakers
6. A CPU (Central Processing Unit) contains an ALU (Arithmetic Logic Unit), control unit, and registers.
7. A processor with two cores is called a dual-core processor and four cores is called a quad-core processor.
8. The control unit determines the sequence in which instructions are executed.
9. The control unit is primarily responsible for movement of data and instructions from itself to the ALU and registers and back.
10. The program counter holds the address of the instruction being processed at the time and the instruction register holds the instruction itself.
True or false: to display the last twenty lines of the text file, afile.txt, you would type tail afile.txt.
Answers
Answer:
True
Explanation:
I come from a family of lines of text
What is the relation, if any, between a web master and a web developer?
A) They are simply different titles that different companies may use for the exact same job.
B) While a web developer maintains a company's websites, the web master creates them in the first place.
C) There is no relation between them as they handle entirely different aspects of a company's web presence
D) While a web master maintains a company's websites, the web developer creates them in the first place.
Answers
Answer:
a)
Explanation:
they are the same
Once a business determines that change needs to occur, what ahould the
business create?
A. Business operation
B. Business analysis
C. Business model
D. Business strategy
Answers
Answer:
D. Business strategy
Explanation:
Kono Dio Da!!
if you were giving a presentation there were 35 people in the room including yourself and you were to shake every person's hand in the room would you shake 35 hands. is it true or false?
Answers
Answer:
False, unless you were to shake your own hand.
Explanation:
does fake news impact our lives
Answers
Answer:
No
Explanation:
because, its fake and not real, and only rean news has a big impact in our lives because we know what is happening around the world
Regardless of how much someone may tell you about their favorite feed aggregator or RSS, you can't tell how well you will like it until you try it yourself. Do you have some favorite RSS readers? Into which category do they fall: productivity, social media, navigation, or business? Pick three of the RSS readers we have discussed, or find other appropriate RSS aggregators that you would like to introduce to your class, and use them to systematically compare the information you find. You are going to need to compare feeds from at least five days; two weeks would be best.
Use your real interests to "load" each reader with the same sites, newspapers, blogs, and so on, and compare the results each day. If one reader has a capability shared by the other two, be sure to set the same parameters. You cannot make a responsible comparison without comparing the same criteria.
As you learn about new features in one reader, add them to the other two (if possible). Keep careful and detailed notes. Record the results and make a five-to seven-minute written report supported by a PowerPoint comparison, complete with screenshots and commentary. At the end of your report period, you should have a preference and solid reasons for your decisions. If challenged, you should be able to prove your point.
Assignment Guidelines:
Evaluate three or more RSS readers over at least five days.
Take detailed notes on your findings.
Report about what you have discovered and relate it to technologies. Present your report in a five-to seven-minute written presentation supported by a PowerPoint comparison, complete with screenshots and commentary.
Answers
The upper class of common RSS lectors that you grant permission find valuable are:
Feedly - falls under the output categoryInoreader - falls under the output typeThe Old Reader - falls under the traveling typeWhat is the RSS readers?Others are:
Flipboard - falls under the friendly television classificationNewsBlur - falls under killing categoryNewsBlur:Note that NewsBlur is a feature-rich RSS editor that offers a range of customization alternatives, containing the capability to create ritual filters and rules. It further offers public facial characteristics that admit you to share and examine items accompanying additional consumers.
Learn more about RSS readers from
https://brainly.com/question/12810862
#SPJ1
what are super computers? what is their application in real life situation
Answers
Answer:
A supercomputer is a computer with a high level of performance as compared to a general-purpose computer. Common applications for supercomputers include testing mathematical models for complex physical phenomena or designs, such as climate and weather, evolution of the cosmos, nuclear weapons and reactors, new chemical compounds (especially for pharmaceutical purposes), and cryptology.
people who use a/an ________________ design logic believe that the given context determines what type of communication is appropriate.
Answers
People who use a/an contextual design logic believe that the given context determines what type of communication is appropriate.
Contextual design logic emphasizes the importance of considering the specific situation, environment, and audience when determining the most effective and appropriate means of communication. It recognizes that different contexts require different communication strategies and channels to convey information effectively.
By adopting a contextual design logic, individuals or organizations take into account factors such as cultural norms, social dynamics, communication goals, and the characteristics of the intended recipients. This approach helps ensure that the communication is tailored to the specific context, taking into consideration factors such as language, tone, medium, and level of formality.
Contextual design logic encourages a more nuanced and adaptable approach to communication, recognizing that what may be suitable in one context may not be effective or appropriate in another. It promotes sensitivity and responsiveness to the context in order to achieve clear, meaningful, and impactful communication.
learn more about "communication ":- https://brainly.com/question/28153246
#SPJ11
HELP ME ⚠️‼️⚠️‼️ DUE IN EXACTLY 27 MINUTES
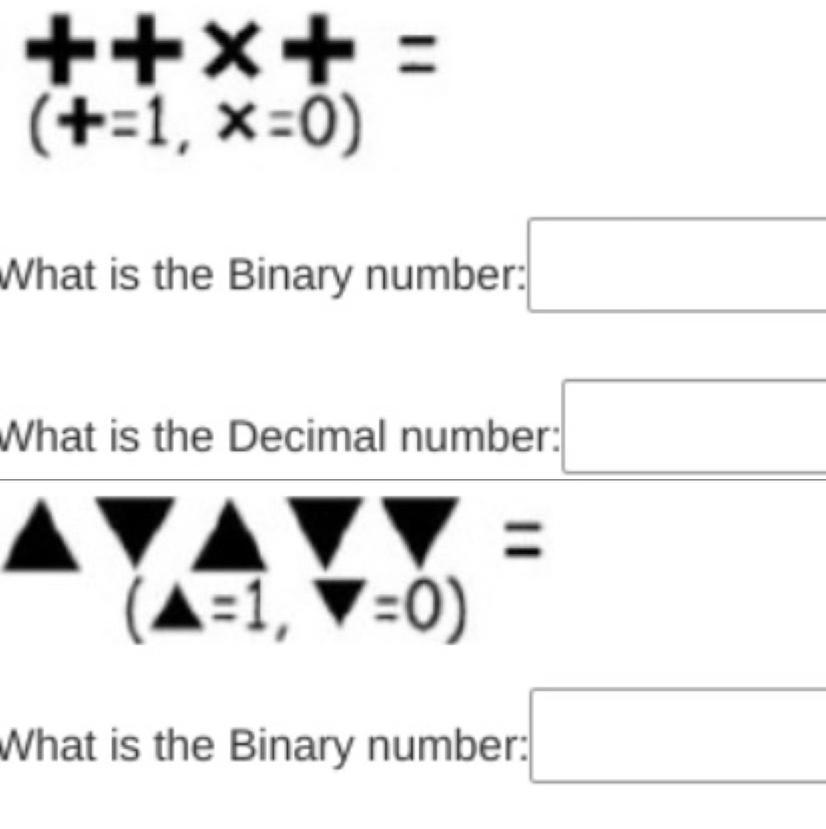
Answers
Answer:
the binary for the first one is 1101
and the binary for the second one is 10100
Explanation:
What are some of the general components of an IDE?
Answers
Answer:
An IDE normally consists of a source e editor, build automation tools. Most modern IDEs have intelligent code completion. Some IDEs contain a compiler, interpreter, or both.
Which of the following describes an action that serves a goal of equity
Answers
Answer:
Please complete your sentence for me to answer.
The Treaty of ______________ laid the foundation for further forms of cooperation in foreign and defense policy among European nations, including a common currency.
Answers
The Treaty of Maastricht laid the foundation for further forms of cooperation in foreign and defense policy among European nations, including a common currency.
Which treaty laid the foundation for further forms of cooperation in foreign and defense policy among European nations, including a common currency?The Treaty of Maastricht, also known as the Treaty on European Union, is an important international agreement that was signed in Maastricht, the Netherlands, in 1992. This treaty marked a significant milestone in the process of European integration and laid the foundation for further forms of cooperation among European nations.
One of the key aspects of the Treaty of Maastricht was the establishment of the European Union (EU), which aimed to deepen political and economic integration among its member states. The treaty introduced several important policies and mechanisms that promoted cooperation in various areas, including foreign and defense policy.
In terms of foreign policy, the treaty outlined the development of a Common Foreign and Security Policy (CFSP) within the EU. This meant that member states would work together to formulate and coordinate their positions on international issues, including diplomatic efforts, crisis management, and peacekeeping operations. The treaty emphasized the importance of common action and solidarity among EU member states in the realm of foreign affairs.
Additionally, the Treaty of Maastricht paved the way for the introduction of a common currency, the Euro. While the implementation of the Euro occurred later, the treaty established the framework for the creation of a single currency among participating EU member states. The Euro has since become the official currency of numerous European countries, promoting economic integration and facilitating cross-border trade and transactions.
Overall, the Treaty of Maastricht was a crucial step in European integration, expanding the scope of cooperation among member states beyond economic matters to encompass foreign policy and defense. It laid the groundwork for the development of the EU as a political and economic union and set the stage for further integration efforts in subsequent treaties and agreements.
Learn more about European nations
brainly.com/question/1683533
#SPJ11
a pneumatic lockout/tagout uses a _________ to prevent use .
Answers
Answer:
Lockable Valve
Explanation:
A pneumatic lockout/tagout typically uses a lockable valve to prevent the use of machinery or equipment.
it is a good idea to maintain duplicate records in different locations for ease of access.
A. True
B. False
Answers
It is true to state that it is a good idea to maintain duplicate records in different locations for ease of access. Option A).
What are duplicate records?It is best to keep duplicate records in different locations for easy access. Penalties for unlawfully or unintentionally removing, damaging, altering, or destroying federal records, or attempting to do so, include fines, imprisonment, or both.
Permanent records are designated as the most important records of the federal government and are maintained permanently. They can never be destroyed! Temporary records are destroyed after a certain time or event.
Learn more about Duplicate Records;
https://brainly.com/question/12112545
#SPJ1
In Python: Write a program to input 6 numbers. After each number is input, print the smallest of the numbers entered so far.
Sample Run:
Enter a number: 9
Smallest: 9
Enter a number: 4
Smallest: 4
Enter a number: 10
Smallest: 4
Enter a number: 5
Smallest: 4
Enter a number: 3
Smallest: 3
Enter a number: 6
Smallest: 3
Answers
Answer:
python
Explanation:
list_of_numbers = []
count = 0
while count < 6:
added_number = int(input("Enter a number: "))
list_of_numbers.append(added_number)
list_of_numbers.sort()
print(f"Smallest: {list_of_numbers[0]}")
count += 1
application of ai in agriculture
Answers
Answer:
Robots for Agriculture: Businesses are creating and programming autonomous robots to perform crucial agricultural tasks, such as harvesting crops more quickly and in greater quantities than human laborers.Crop and Soil Monitoring: Businesses are using computer vision and deep-learning algorithms to process data obtained from drones and/or software-based technology to keep track of the health of their crops and soil.Machine learning (ML) models are being developed to monitor and forecast the effects of various environmental factors, such as weather changes, on crop yield.Emerging AI-driven technologies are addressing industry issues like crop yield, soil health, and herbicide resistance while also helping to increase efficiency. Robotic farming is set to become a highly regarded application of artificial intelligence. It's also conceivable that soon, agricultural robots will be created to carry out a wide range of tasks.
i hope this works......i literally went through the books to find those...lol
Answer:
eriuhewfiuefwuieqwb
Explanation:
which tool is used to terminate cables into a 66-block
Answers
Answer: Circuit pairs are connected to the block with a punch-down tool by terminating the tip wire on the leftmost slot of one row and ring wire on the leftmost slot of the row beneath the mating tip wire.
Write a Java program that prints out a 4x4 square (like the one below)

Answers
public class 4by4Square
{
public static void main(){
System.out.println("xxxx \nx x\nx x\nxxxx");
}
}
~CaptnCoderYankeeQUESTION 4
Which of the following needs to be conducted to ensure the
security of a database is being maintained?
a. Data audit
b. Data modelling
c. Data decryption
d. Data enc
Answers
Answer:
Explanation:
To ensure the security of a database is being maintained, a data audit*needs to be conducted.
A data audit is a systematic examination and evaluation of data-related activities and processes to assess compliance with security policies, identify vulnerabilities, and detect any unauthorized access or breaches. It involves reviewing data access controls, permissions, user activities, and data storage practices to ensure the integrity, confidentiality, and availability of the database.
While data modelling, data decryption, and data encryption are important aspects of database management and security, they do not directly address the ongoing maintenance and monitoring of database security. Data modelling refers to the process of designing the structure and relationships of data within a database. Data decryption involves converting encrypted data back to its original form, while data encryption is the process of converting data into a form that is unreadable without the appropriate decryption key.
In contrast, a data audit is specifically focused on evaluating the security measures and practices in place to protect the database from unauthorized access, data breaches, and other security threats.
Learn more about data auditing and database security practices to ensure the robustness and protection of your database systems.
https://brainly.in/question/3494380
#SPJ11
What is the missing line of code?
class shoe:
self.style = style
self.color = color
def __str__(self):
return self.style + ' ' + self.color
Answers
Answer:
def_init_(self, style, color):
explanation:
i just took the test on edg 2020
The missing line of code is def_init_(self, style, color).
What is code?Code is defined as the instructions written in a programming language that a compiler transforms into computer code. Although a code technically lacks a defined meaning, doctors frequently use it to refer to a cardiopulmonary arrest that occurs to a patient in a hospital or clinic and necessitates the prompt arrival of a team of medical professionals and the start of resuscitative measures.
The code is complete and in perfect working order. The Person class is properly extended from the Employee class. As a result, Person is the parent class of Employee and Employee is a subclass of Person. The only issue with this code is its flawed structure, which includes missing whitespace and indexing, two essential Python features.
Thus, the missing line of code is def_init_(self, style, color).
To learn more about code, refer to the link below:
https://brainly.com/question/497311
#SPJ5