In Python, what kind of error is returned by the following code? (e. G. NameError, ValueError, IOError, etc. ) def my_func(n1, n2): return n1 + n2 my_func(1, 2, 3)
Answers
The code will raise a TypeError error.
The my_func() function is defined to accept two parameters (n1 and n2), and returns their sum. However, when the function is called with three arguments (1, 2, and 3) on the third line, a TypeError error is raised. This is because the function was called with too many arguments, and Python does not know how to handle the extra argument.
A TypeError error occurs when an operation or function is applied to an object of inappropriate type. In this case, the function was called with the wrong number of arguments, which results in a TypeError being raised.
To know more about code click here:
brainly.com/question/497311
#SPJ4
Related Questions
200 points if answered correctly. Including variability in your video games is completely unnecessary and adds nothing to the player’s experience.
Group of answer choices
True
False
Answers
........
my guess is false.
Answer:
true
Explanation:
Can someone please answer this? It isn't Insert

Answers
Answer:
The answer for this question is b Add to
A. Application based questions. 1. Samay works as an accountant at a school. He has installed Tally on his computer which will help him with maintaining accounts. Which type of software is Tally?
Answers
Tally is an example of accounting software used by Samay, the accountant at a school, to maintain accounts.
Tally is categorized as accounting software. Accounting software is designed specifically for managing financial transactions, record keeping, and generating financial reports. It automates various accounting tasks such as bookkeeping, ledger management, invoicing, inventory management, and financial analysis.
Tally provides features and functionalities that are tailored to meet the specific needs of accountants and financial professionals.With Tally, Samay can efficiently record financial transactions, create balance sheets, track income and expenses, manage payroll, generate financial reports, and perform other accounting-related tasks. The software simplifies the process of maintaining accurate and up-to-date financial records, ensuring compliance with accounting standards and regulations.Tally's user-friendly interface and comprehensive functionalities make it a popular choice for businesses and professionals in various industries, including educational institutions like schools.
For more questions on Tally
https://brainly.com/question/32636753
#SPJ8
Briefly discuss the aesthetics and ergonomics of a hydraulic jack. First explain what these
terms mean and then discuss their application on a hydraulic jack.
Answers
Answer:
For this model, aesthetics is defined as a measure of how attractive a product appears, and ergonomics is how well a product feels when used/held. ... Two important types of defects, part flash and crush, will be used to define ergonomic and aesthetic PA's, respectively.
----------------------------
Please summarize into 1.5 pages only
----------------------------
Virtualization
Type 2 Hypervisors
"Hosted" Approach
A hypervisor is software that creates and runs VM ins
Answers
Virtualization: It is a strategy of creating several instances of operating systems or applications that execute on a single computer or server. Virtualization employs software to reproduce physical hardware and create virtual versions of computers, servers, storage, and network devices. As a result, these virtual resources can operate independently or concurrently.
Type 2 Hypervisors: Type 2 hypervisors are hosted hypervisors that are installed on top of a pre-existing host operating system. Because of their operation, Type 2 hypervisors are often referred to as "hosted" hypervisors. Type 2 hypervisors offer a simple method of getting started with virtualization. However, Type 2 hypervisors have some limitations, like the fact that they are entirely reliant on the host operating system's performance.
"Hosted" Approach: The hosted approach entails installing a hypervisor on top of a host operating system. This hypervisor uses hardware emulation to create a completely functional computer environment on which several operating systems and applications can run concurrently. In general, the hosted approach is used for client-side virtualization. This method is easy to use and is especially useful for the creation of virtual desktops or the ability to run many operating systems on a single computer.
A hypervisor is software that creates and runs VM instances: A hypervisor, also known as a virtual machine manager, is software that creates and manages virtual machines (VMs). The hypervisor allows several VMs to execute on a single physical computer, which means that the computer's hardware can be utilized more efficiently. The hypervisor's role is to manage VM access to physical resources such as CPU, memory, and I/O devices, as well as to provide VM isolation.
Know more about virtualization, here:
https://brainly.com/question/31257788
#SPJ11
Write the definition of a method printAttitude, which has an int parameter and returns nothing. The method prints a message to standard output depending on the value of its parameter.
Answers
Answer:
void printAltitude(int alt) {
printf("Current altitude is %i meters.", alt)
}
Explanation:
First declare the function saying that it won't return anything (void), then you say thatbit uses one parameter that is a Integer number (int). This parameter is stored as "alt", that you use it to print a new line by formatting it with %i.
Which of the following is true concerning derivative classification? Select one: a. Only appointed individuals may perform derivative classification. b. Derivative classifiers are responsible for analyzing and evaluating information to identify elements that require classification. c. Consulting the Original Classification Authority (OCA) is the first step in the derivative classification process. d. Photocopying a Secret document is an example of derivative classification.
Answers
The true statement about concerning derivative classification is ---Derivative classifiers are responsible for analyzing and evaluating information to identify elements that require classification.
Option B is correct.
What is Derived Classification?“Derivative classification” means incorporating, paraphrasing, rephrasing, or creating in a new form information that has already been classified and marking newly developed material in accordance with the classification markings applied to the source information. increase.
What is the significance of derivative classification?Readers can infer classified information by performing additional interpretations or analyses. Derivative Classifiers are responsible for forwarding classification guidance and applicable downgrade and declassification instructions.
Who can be a derived classifier?A person authorized to certify that an unmarked document or material is unclassified or to determine that it has been classified as acceptable according to the authority's designation.
Learn more about derivative classification:
brainly.com/question/14294203
#SPJ4
your company uses two applications that publish the following apis: app1 publishes 30 apis that reside on five servers. app2 publishes 40 apis that reside on 10 servers. you need to implement an azure api management solution. the solution must provide full functionality for both applications. what is the minimum number of apis that you must publish in azure api management?
Answers
The minimum number of APIs that you must publish in Azure API Management is 70.
What is the APIs about?To implement an Azure API Management solution for both applications, you will need to publish all of the APIs from both App1 and App2 in Azure API Management. Therefore, the minimum number of APIs that you must publish in Azure API Management is:
30 APIs from App1 + 40 APIs from App2 = 70 APIs
Therefore, You will need to configure the API Management instance with the 70 APIs, including any required policies, security measures, and rate limits. Additionally, you will need to configure the instance to route traffic to the appropriate backend servers hosting the APIs.
Learn more about APIs from
https://brainly.com/question/12987441
#SPJ1
See full qustion below
Your company uses two applications that publish the following APIs: App1 publishes 30 APIs that reside on five servers. App2 publishes 40 APIs that reside on 10 servers. You need to implement an Azure API Management solution. The solution must provide full functionality for both applications. What is the minimum number of APIs that you must publish in Azure API Management? Select only one answer. 2 15 70 450
Examples of vector graphics include Select all that apply. A. logos B. blueprints C. photos D typefaces
Answers
Examples of vector graphics include A. logos and B. blueprints. Vector graphics are created using mathematical equations and can be scaled up or down without losing their quality. Logos and blueprints are often created as vector graphics because they need to be precise and scalable.
Photos and D. typefaces, on the other hand, are not examples of vector graphics. Photos are raster images, which are made up of pixels, and cannot be scaled up without losing quality. Typefaces, while they can be created as vector graphics, are typically used as raster images in digital media and print. In summary, the examples of vector graphics include logos and blueprints.
examples of vector graphics include: Logos, Blueprints, By configuring the settings, users can set restrictions on who can access certain files or applications, which devices can connect to the computer, and what actions can be performed on the computer. By implementing the security policies, users can increase the overall security of their computer and prevent potential security breaches. True. The Task Scheduler is a tool in Windows operating systems that allows users to automate tasks on their computer. Users can schedule tasks to run at specific times or intervals, start programs or scripts, and stop services. The Task Scheduler can help users save time and improve productivity by automating repetitive tasks. Additionally, users can also use the Task Scheduler to perform maintenance tasks such as system backups or updates. Overall, the Task Scheduler is a useful tool that can help users streamline their workflow and improve the efficiency of their computer.faces Vector graphics are commonly used for these types of designs because they can be easily resized without losing quality. Photos (C) are not vector graphics, as they are raster images composed of pixels.
To know more about graphics visit:
https://brainly.com/question/14191900
#SPJ11
A method of changing unproductive thoughts into constructive ones is called
meditation.
visualization.
positive self-talk.
deep breathing.
Answers
A method of changing unproductive thoughts into constructive ones is called meditation. Hence, option A is correct.
What is unproductive thoughts?An inclination or habit is a mindset that doesn't offer any benefits, effects, or results. Such a mindset pulls the client's focus away from his goals, fulfillment, and empowerment. Negative thoughts may be part of an unproductive mindset.
Overthinking, sometimes referred to as rumination, is when you keep returning to the same idea or event in your mind until it starts to interfere with your life. The two primary forms of overthinking are worrying about the future and brooding on the past.
People who have previously faced difficulty for which they were unprepared may get into the habit of catastrophizing.
Thus, option A is correct.
For more information about unproductive thoughts, click here
https://brainly.com/question/16875515
#SPJ6
Answer:positive self talk
Explanation:
essay on the importance of computer and internet 250 word
Answers
With the significant progress in technology, the importance of the internet has only multiplied with time. The dependence on the internet has been because of multiple advantages that it has to offer – for instance reducing the work stress and changing the face of communication most importantly. By employing the correct usage of the internet, we can find various information about the world. The internet hosts Wikipedia, which is considered to be one of the largest best-composed reference books kept up by a vast community of volunteer scholars and editors from all over the world. Through the internet, one may get answers to all their curiosity. In the education sector too, it plays a major role, especially taking into consideration the pandemic. The Internet during the pandemic provided an easy alternative to replace the traditional education system and offers additional resources for studying, students can take their classes in the comforts of their homes. Through the internet, they can also browse for classes – lectures at no extra cost. The presence of the internet is slowly replacing the use of traditional newspapers. It offers various recreational advantages as well. It can be correctly said that the internet plays a great role in the enhancement of quality of life.
Answer:
Computers and the internet are highly prevalent and crucial in our everyday lives since they are the method by which the current enormous world is linked and becomes one. Computers have altered human life by making things faster and more efficient. Individuals may generate, store, and retain data. Computers and the internet are used by businesses in a variety of areas, including banking, retail, education, and so on. Because of the rising technical capabilities of Internet connectivity, the processing and utilization of information and knowledge is becoming extremely important for society. Since the dawn of the modern era, the Internet has been an outstanding tool for global informatization. It is a fair and accessible source of varied information as well as a mechanism of knowledge dissemination. Computers are incredibly significant today since they are very precise, speedy, and can effortlessly do numerous jobs. Manually doing those activities would take significantly more time. It can perform extremely complex computations in a fraction of a second. Furthermore, it can hold a large quantity of data. One may obtain a variety of knowledge about the globe by using the internet correctly. The internet can provide answers to all of one's questions. It also plays an important part in the education sector since it is an easy alternative to the traditional education system and provides additional learning materials; students may attend their lectures from the comfort of their own homes. They may also search for lessons and lectures on the internet for free.
Technician A states that in a brake-by-wire system, the computer detects a
panic stop if the driver quickly releases the accelerator. Technician B states
that brake-by-wire systems are not efficient in detecting panic stops. Who is
correct?
O a. Technician A
O b. Technician B
O c. Both Technician A and Technician B
O d. Neither Technician A nor Technician B
Answers
The brake-by-wire system can detect panic stops if the driver abruptly releases the accelerator, so Technician A is only partly accurate. Technician B is mistaken because panic stops can be accurately detected by brake-by-wire devices.
How well do brake-by-wire devices work at spotting panic stops?That period of time and distance can be cut down in a brake-by-wire device. The driver's abrupt release of the accelerator can be detected by the computer, which could be a sign of a panic halt.
What does an anti-lock braking device (MCQ) do?In order to keep tractive contact with the road surface and give the driver more control over the car, ABS works by preventing the wheels from locking up when braking.
To know more about panic stops visit:
https://brainly.com/question/28779956
#SPJ9
PLEASE HELPPPPPPP
Flight Time
You need to calculate the flight time of an upcoming trip. You are flying from LA to Sydney, covering a distance of 7425 miles, the plane flies at an average speed of 550 miles an hour.
Calculate and output the total flight time in hours.
Hint
The result should be a float.

Answers
Answer:
Time taken by plane = 13.5 hour
Explanation:
Given:
Total distance cover by plane = 7,425 miles
Average speed of plane = 550 miles per hour
Find:
Time taken by plane
Computation:
Time taken = Distance / Speed
Time taken by plane = Total distance cover by plane / Average speed of plane
Time taken by plane = 7,425 / 550
Time taken by plane = 13.5 hour
The calculation and output the total flight time in hours is represented as follows:
def time(distance, speed):
time = distance / speed
print(time)
time(7425, 550)
speed = distance / time
time = distance / speed
We used function in python to determine the flight time. The function name is time.
The arguments are distance and speed.
Then we declare the mathematical formula to calculate the time of flight.
The we print the time of flight.
The function is called with its arguments, distance and speed.
The answer should be 13.5 hours and the output should be 13.5.
learn more ; https://brainly.com/question/23746890?referrer=searchResults

What is the difference between a class and an object in Python?
Answers
Answer: A class is a template for creating Python objects within a program, whereas the object itself is an instance of the Python class. You can think of a class as a blueprint for an object that includes the available functions and data variables.
Explanation:
A collection of data (variables) and methods (functions) that act on those variables constitutes an object. A class, similarly, is a blueprint for that object. A class can be compared to a rough sketch (prototype) of a house.
Some applications require that records be retrievable from anywhere in the file in an arbitrary sequence. These files are known as ___________.
Answers
Answer:
random access files
Explanation:
Some applications require that records be retrievable from anywhere in the file in an arbitrary sequence. These files are known as ___________.
✓ RANDOM ACCESS FILES
In ten sentences, briefly describe Artificial Intelligence
Answers
The Windows _________ feature allows you to install patches to maintain the security of your computer.
Answers
virtual conections with science and technology. Explain , what are being revealed and what are being concealed
Answers
Some people believe that there is a spiritual connection between science and technology. They believe that science is a way of understanding the natural world, and that technology is a way of using that knowledge to improve the human condition. Others believe that science and technology are two separate disciplines, and that there is no spiritual connection between them.
What is technology?
Technology is the use of knowledge in a specific, repeatable manner to achieve useful aims. The outcome of such an effort may also be referred to as technology. Technology is widely used in daily life, as well as in the fields of science, industry, communication, and transportation. Society has changed as a result of numerous technological advances. The earliest known technology is indeed the stone tool, which was employed in the prehistoric past. This was followed by the use of fire, which helped fuel the Ice Age development of language and the expansion of the human brain. The Bronze Age wheel's development paved the way for longer journeys and the development of more sophisticated devices.
To learn more about technology
https://brainly.com/question/25110079
#SPJ13
You have been on the phone with a user in a remote office for 30 minutes troubleshooting their minor desktop problem. No matter how many times you explain the solution to them, they do not understand what you are saying. What should you do?
A. Go to the user's site
B. Suggest they call back tomorrow
C. Suggest they call another technician
D. Suggest you talk to their manager
Answers
Answer:
D
Explanation:
First when you are troubleshooting a client your main goal is to solve their issue, you dont want to say hey call later i cant help you or say call someone else because picture this you need help and someone hangs up on you or says (B.) or (C.) it comes off as rude i would say. Regarding (A.) im not 100% sure what exactly do you mean by user's site? But asking for their manager (D.) or someone else (preferably higher up) seems to be the right action to be taken.
The phone with a user in a remote office for 30 minutes troubleshooting their minor desktop problem. D. Suggest you talk to their manager
How do you resolve troubleshooting problems?To run a troubleshooter:
Select Start > Settings > Update & Security > Troubleshoot, or select the Find troubleshooters shortcut at the end of this topic.
Select the type of troubleshooting you want to do, then select Run the troubleshooter.
Allow the troubleshooter to run and then answer any questions on the screen.
To learn more about troubleshooting desktop problem, refer
https://brainly.com/question/15714846
#SPJ2
Read the mini case study below. It documents a project’s (in some cases catastrophic) failure. In light of this module’s topics, discuss two contributing factors to the failure of this project.
Organization: Dyson Ltd – UK
Project type: Development of an electric car
Project name: The Dyson
Date: Oct 2019
Cost: £500M
Synopsis:
The future of transportation is here to see and it is of course electric! As a result, the development of electric cars has been a growth area for the past ten years and the pace of change continues to grow.
That growth and the potential to revolutionize the car market has interested both newcomers and the incumbents alike. Of the newcomers Tesla has of course made the cut and has proven they have the stamina to stay in the game. Other start-ups and have come, gone, been resurrected and gone again. At the time of writing Rivian, Fisker and other start-ups are still in the game, but they face the monumental challenge of taking on the likes of Volkswagen, Nissan, GM and other organizations that already have the infrastructure to design, build, sell and support vehicles on a worldwide basis.
One of the recent challengers to throw in the towel is Dyson Ltd. James Dyson is one of the UK richest men. An engineer, a techie and an entrepreneur, Dyson made his fortune developing high-end home appliances (most notably vacuum cleaners). Always looking for fields in need of his engineering prowess, Dyson started down the difficult road of developing a from-scratch electric car. The jump from vacuum cleaners to cars is of course massive and the decision to invest in the project was a quantum leap of faith.
Normally such a move would require careful due diligence and active management of the downside risks. It appears, however, that as a privately owned business, Dyson took a different path. In a Mar 2020 interview with business magazine "Fast Company" Dyson was asked about the role up front market analysis plays in developing Dyson products. Dyson replied…
"We never think of the market for the product. It’s not something that guides us. We look for a problem in the product, and then we go to solve the problem. Hand dryers aren’t a particularly big market compared to hair dryers or vacuum cleaners, but that didn’t stop us from wanting to make a hand dryer. Having an interesting technology for products decides what we do, whether the market is small or big."
To be fair, Dyson’s leap of faith did make a lot of progress and reports indicate that his nascent project got as a far as a fully functional vehicle that was near ready for production. However, as costs mounted past the £500M mark, the monumental costs of product launch came into view. Recognizing that to cover the investment and production costs the finished product was likely to have a price higher than the market would bare, the project has been canned.
Note: Dyson is a privately owned company and the cost of the project was apparently born by Mr. Dyson himself. Although Mr. Dyson can certainly afford to absorb the £500M cost, I think we should also remember the time, talent, sweat and tears of the team who work on the project. To see all of that effort wasted is a heart break in its own right. Hopefully some of the technology will still find a way forward and some of that effort will be rewarded, but as it stands, the project may not be catastrophic for Dyson, but it is likely a massive disappointment for those who vested themselves in the project’s success.
Answers
The failure of the Dyson electric car project can be attributed to a combination of factors. The lack of thorough market analysis and consideration of the competitive landscape prevented Dyson from adequately positioning their product in the automotive market.
Two contributing factors to the failure of the Dyson electric car project are:
Lack of market analysis and consideration of competitive landscape:
Dyson's approach of focusing primarily on solving a problem rather than considering the market demand and competition played a significant role in the project's failure. The decision to develop an electric car without thoroughly analyzing the market and understanding the challenges posed by established automotive manufacturers with global infrastructure put Dyson at a disadvantage. While Dyson had a track record of innovation and success in the home appliances industry, the automotive sector is highly complex and competitive. Not adequately assessing the market dynamics and competition hindered their ability to develop a competitive product and establish a viable market position.
Mounting costs and pricing challenges:
Although the project made substantial progress and reached the stage of a fully functional vehicle near production readiness, the costs associated with launching the product became a significant concern. As the costs exceeded £500 million, the realization that the final product would likely have a price higher than what the market would bear posed a major obstacle. Dyson's decision to halt the project can be attributed to the realization that the financial viability of the electric car was questionable due to the high production costs and anticipated pricing challenges. Failing to align the project's costs with market expectations and feasible pricing strategies contributed to its ultimate discontinuation.
The failure of the Dyson electric car project can be attributed to a combination of factors. The lack of thorough market analysis and consideration of the competitive landscape prevented Dyson from adequately positioning their product in the automotive market. Additionally, the mounting costs and pricing challenges posed significant financial risks and made the project economically unviable. While the project may not have had catastrophic consequences for Dyson as a company, it was undoubtedly a disappointment for the team involved and a missed opportunity to leverage their technological advancements in the automotive industry.
To know more about electric car visit
https://brainly.com/question/30016414
#SPJ11
What type of access point is configured by an attacker in such a manner that it mimics an authorized access point
Answers
Answer:
Evil twin AP
Funny name, yes, but this is actually a not-so-funny term for an AP set up by an attacker, mimicking your AP, and using this method to attack your client devices and networks.
Please thank me if you are reading this, and have a good day.
TRUE OR FALSE 84) Organizations can use existing network security software to secure mobile devices.
A) TRUE
B) FALSE
Answers
True, organizations can use existing network security software to secure mobile devices. It is important for organizations to protect their networks and data from unauthorized access, and this includes securing mobile devices that connect to their systems. Using network security software can help monitor, detect, and prevent potential security threats from affecting mobile devices and the overall network. By extending security measures to mobile devices, organizations can maintain a strong security posture and reduce the risk of cyber-attacks.
In conclusion, organizations can use existing network security software to secure mobile devices, but it is important to ensure that the software is configured to address the unique vulnerabilities of mobile devices and that additional security measures are implemented as needed.
Know more about network security software here:
https://brainly.com/question/15393655
#SPJ11
if Z ~N( 0, 1) compute following probabilities:
a. P(Z≤1.45)
b. P( -1.25 ≤ Z ≤ 2.3)
Answers
a. The value of P(Z ≤ 1.45) is 0.9265
b. The value of P(-1.25 ≤ Z ≤ 2.3) is 0.8837.
From the question above, Z ~ N(0, 1)
We need to find the following probabilities:
a. P(Z ≤ 1.45)
From the standard normal distribution table, we can find that P(Z ≤ 1.45) = 0.9265
Therefore, P(Z ≤ 1.45) ≈ 0.9265
b. P(-1.25 ≤ Z ≤ 2.3)
From the standard normal distribution table, we can find that:
P(Z ≤ 2.3) = 0.9893 and P(Z ≤ -1.25) = 0.1056
Now we can calculate the required probability as follows
:P(-1.25 ≤ Z ≤ 2.3) = P(Z ≤ 2.3) - P(Z ≤ -1.25)= 0.9893 - 0.1056= 0.8837
Therefore, P(-1.25 ≤ Z ≤ 2.3) ≈ 0.8837.
Learn more about probability at
https://brainly.com/question/31909306
#SPJ11
add an if branch to complete double_pennies()'s base case. sample output with inputs: 1 10 number of pennies after 10 days: 1024
Answers
The given function is incomplete and needs to be modified to get the correct output. The function name is `double_pennies()` and it is missing an if-else statement.
It takes in two arguments, `num_of_pennies` and `num_of_days`.The function doubles the number of pennies every day and returns the total number of pennies at the end of the given days.
The base case of the function has to be added to get the correct output for lower values of days, so the function looks like this:```def double_pennies(num_of_pennies, num_of_days):
if num_of_days == 0:
return num_of_pennies else:
return double_pennies(num_of_pennies * 2, num_of_days - 1)``
The above code will return the correct output for the given input of 1 and 10 which is:```number of pennies after 10 days: 1024```
To know more about statement visit:-
https://brainly.com/question/31655355
#SPJ11
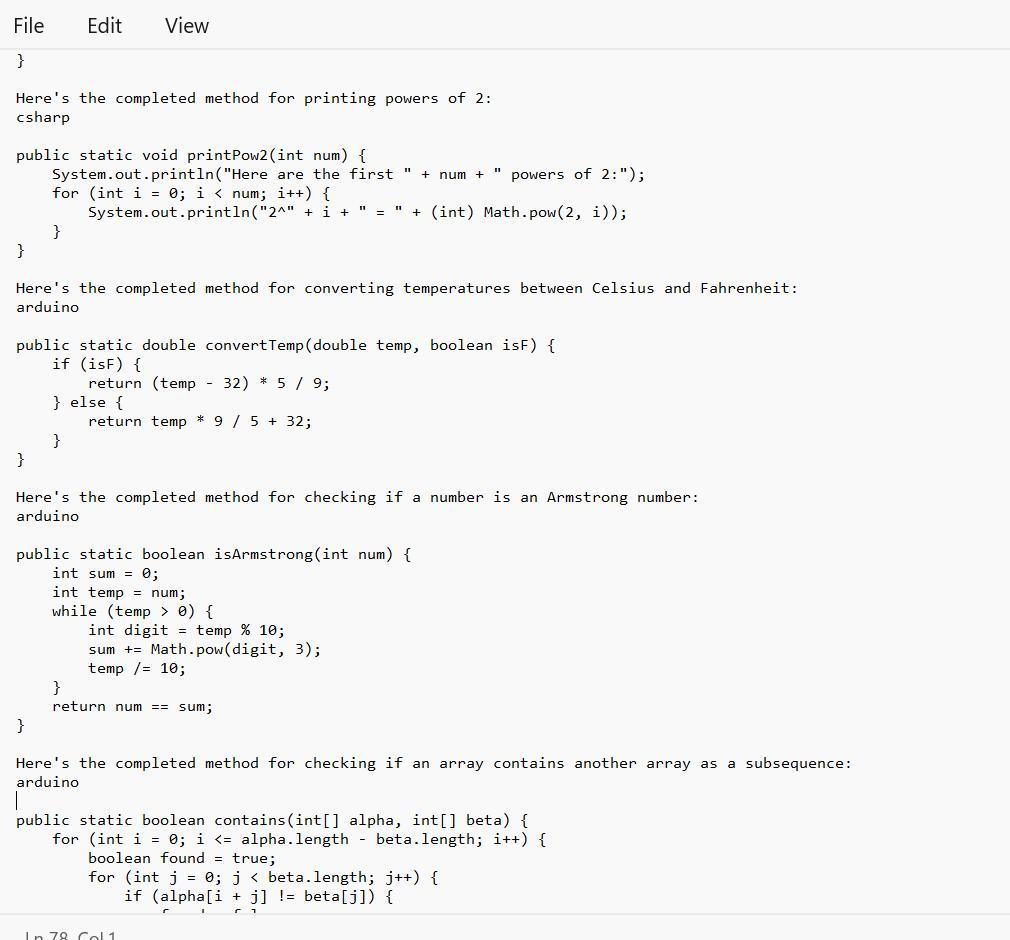
Java Coding help please this is from a beginner's class(PLEASE HELP)
Prior to completing a challenge, insert a COMMENT with the appropriate number.

Answers
Given in the images are the completed method that one can be able to use for a linear search on an array:
What is the Java Coding?The given text provides several programming code that bear completing the work of different styles.
Note tnat Each system has a specific set of conditions that need to be met in order to give the anticipated affair.
Therefore, code range from simple codes similar as performing a direct hunt on an array or publishing a board with a given size and pattern, to more complex codes similar as checking if one array contains another array in a successive and ordered manner.
Learn more about Java Coding from
https://brainly.com/question/18554491
#SPJ1
See text below
1) Complete the method: public static int simpleSearch(int[] nums, int value), that performs a linear (sequential) search on the array parameter, and returns the index of the first occurrence the of value parameter. Return -1 if value doesn't exist in nums.
simpleSearch(new int[] {8, 6, 7, 4, 3, 6, 5), 7) >>> 2
//2 is index of the value 7
2) Complete the method: public static void squareBoard(int num), that prints an num by num board with a '#' character in every position.
squareBoard(2) >>>
3) Complete the method: public static void checkerBoard(int num), that prints an num by num board with a '# character in every position in a 'checkerboard' fashion.
checker Board(3) >>>
4) Complete the method: public static void printPow2(int num), that prints num powers of 2 (including O), given the supplied number. Use String concatenation to print like this:
//with a call of printPow2(4):
Here are the first 4 powers of 2:
2^8 = 1
2^1 = 2
2^2 = 4
238
5) Complete the method: public static double convertTemp/double temp, boolean isF), that performs a Celsius to Fahrenheit conversion (and vice versa) when called. The parameter isF will be supplied as true if temp is in Fahrenheit.
6) Complete the method: public static boolean isArmstrong(int num), that returns true if the supplied number is an "Armstrong number". An Armstrong number is a number for which the sum of the cubes of its digits is equal to the number itself. Modulus and integer division will help.
IsArmstrong (371) >>> true //3*3*3+7*7*7+ 1*1*1 == 371
7) Difficulty level HIGH: Complete the method: public static boolean contains(int[] alpha, int[] beta). that returns true if the sequence of elements in beta appear anywhere in alpha. They must appear consecutively and in the same order. You'll need nested loops for this.
contains(new int[] {1, 2, 1, 2, 3), new int[] {1, 2, 3}) >>> true
contains (new int[] 1, 2, 1, 2, 3, 1), new intf (1, 1, 3, 1)) >>> false


Which method below is a physical security measure?
A firewall
Passwords
Anti-virus
helpp!
Answers
The only given option that is a physical security measure is; Passwords
Computer Security
Physical security is defined as the protection of personnel, hardware, software, networks or data from the adverse effect of human actions and events. These adverse actions or events could lead to severe loss and damage to an enterprise or any institution or even personnel.
Now, among the given options, firewall is a network security that simply monitors and filters the incoming and outgoing network traffic on a computer.
Anti-virus is uses to detect and remove corrupt files from a computer system. Whereas passwords are physical security measures because they involve human actions.
Read about Computer security at; https://brainly.com/question/26260220
A large corporation uses:
A.
LAN
B.
WAN
C.
Wireless network
D.
Ethernet connection
Answers
Answer:
WAN
but im saying this bc you cant mark brainliest with only 1 answer there
Answer:
B: WAN
Explanation:
Explain a situation(s) where bubbles can be used to improve a
sonars performance(1-2 pages)
provide reference
Answers
They can be used to improve sonar's performance in situations where there is a need to enhance the transmission and reception of sound waves underwater.
Bubbles can be used to improve sonar's performance in situations where there is a need to enhance the transmission and reception of sound waves underwater. One such situation is in the field of underwater communications. When sound waves travel through water, they can encounter various challenges such as attenuation, scattering, and interference. These factors can degrade the quality and range of underwater communication systems. By introducing bubbles into the water, the sonar system can exploit their acoustic properties to overcome these challenges and improve signal transmission and reception.
Bubbles can act as scatterers and reflectors of sound waves. When sound waves encounter bubbles, they can be reflected, refracted, or diffracted, depending on the size and distribution of the bubbles. This scattering effect can help in spreading the sound energy over a larger area, reducing the effects of attenuation and increasing the coverage range of the sonar system. Additionally, bubbles can act as resonators, resonating at specific frequencies and enhancing the detection and transmission of signals at those frequencies. This can be particularly useful in situations where specific frequencies are used for underwater communication.
One application where bubbles have been utilized to improve sonar performance is in underwater wireless sensor networks (UWSNs). UWSNs consist of a network of autonomous underwater devices that communicate with each other. In such networks, the presence of bubbles can help in increasing the range and reliability of communication links. Research studies, such as the work by Akyildiz et al. (2011), have investigated the use of bubbles as scattering elements to create bubble-based communication channels in UWSNs. These bubble channels can provide enhanced signal propagation and reduce the effects of fading and interference, leading to improved performance and connectivity in underwater communication systems.
In conclusion, the strategic use of bubbles can significantly enhance sonar performance in underwater communication systems. By exploiting the acoustic properties of bubbles, such as their scattering and resonating effects, it is possible to improve signal transmission, increase coverage range, and mitigate the challenges associated with underwater communication. Further research and development in this area can lead to advancements in underwater communication technologies and their applications in various domains, including marine exploration, underwater robotics, and environmental monitoring.
Akyildiz, I. F., Pompili, D., & Melodia, T. (2011). Underwater acoustic sensor networks: research challenges. Ad Hoc Networks, 9(6), 669-678.
Learn more about transmission here:
brainly.com/question/10604099
#SPJ11
Julian is looking at an outline in Word. Which lines should he look at to see Level 1 text?
the lines farthest to the right
the lines farthest to the left
the top line
the bottom line
Answers
An outline in Word is an ordered list of the main points of a document. The levels of text in an outline correspond to different levels of heading in the document.
Word allows you to use the built-in heading styles to create an outline, or you can manually format your document using indents to create a multilevel list. Using the Outline view in Word helps you focus on the structure of your document. In the Outline view, you can expand or collapse heading levels to show or hide the content beneath them. This can help you get an overview of your document and reorganize it easily. To see Level 1 text, Julian should look at the lines farthest to the left.
Each level of text in an outline corresponds to a specific indentation. Level 1 text is the highest level of text and is usually the main heading of the document. It is displayed in the leftmost column of the Outline view. The other levels of text are indented to the right, with each level of indentation indicating a lower level of importance or subheading.
To know more about outline visit:
brainly.com/question/818528
#SPJ11
Select a key term from the key terms page located in the chapters in the Learn section. Do research on the key term and find an article that relates to the key term. You will provide a definition of the key term and a summary of the selected article related to the key term. You will also provide a discussion in your own words of the article and how it relates to the textbook. Use 2 other outside sources to support your discussion. Then, you will list and annotate all references in the reference section in APA format. The student will post one thread of a minimum of 250 words. Key term: production level output. Acceptable sources include the International section of any reputable website that focuses on international business,
such as Wall Street Journal, Financial Times, or the Economist.
Answers
The key term chosen for this answer is "production level output". It is defined as the total amount of goods and services produced by a firm during a specific period. It is an important concept in business as it helps to determine the efficiency of a company's production processes and its ability to meet demand.
The selected article is "Japan's Industrial Output Rebounds at Fastest Pace in 10 Months" from the Wall Street Journal. The article reports on the increase in Japan's industrial output by 4% in February 2021, which is the fastest pace in ten It also highlights the importance of productivity in achieving economic growth and improving living standards.
Two other sources that support this discussion are:
1. The article "The Importance of Measuring Productivity and Output" by the Balance Small Business. It emphasizes the importance of measuring productivity and output in business operations and the various methods used to do so. This article further highlights the significance of increasing productivity to achieve sustainable economic growth.
2. The article "What Is Production Output?" by Chron. It explains the meaning of production output and how it is calculated. It further highlights the importance of monitoring production output to improve efficiency and reduce costs.
To know more about key term visit:
brainly.com/question/3808019
#SPJ11