bill is a forensic specialist. he is preparing instructions for how to seize evidence from mobile devices. one of the rules is to make sure the examiner does not write to the device. which of the following would ensure that an examiner does not write to the device when connecting it to a windows computer?
Answers
To ensure that an examiner does not write to a mobile device when connecting it to a Windows computer, the examiner should use a write-blocker.
Explanation:
A write-blocker is a hardware or software device that prevents any write commands from being sent to the connected device, thus protecting the integrity of the data on the device. When a mobile device is connected to a Windows computer, the computer may attempt to write data to the device, such as creating temporary files or updating timestamps. This can potentially overwrite or modify data on the device, which can compromise the integrity of the evidence.
By using a write-blocker, the examiner can prevent any write commands from being sent to the device, ensuring that the data on the device remains unaltered during the examination process. This is critical to maintaining the integrity of the evidence and ensuring that any information obtained from the device is admissible in court.
To know more about Windows computer click here:
https://brainly.com/question/28525121
#SPJ11
Related Questions
What is block palette
Answers
When posting a résumé to an employer’s Web site, it is important to follow the directions carefully. Please select the best answer from the choices provided T F
Answers
When posting a resume to an employer’s Website, it is important to follow the directions carefully. This statement was true. Thus, option (a) is correct.
If must standardize your curriculum in order to implement it on a job site. It is taught to on construction sites. Because it makes it easier for hiring companies to read, this is very significant.
In actuality, standardized practices are common in all things that are official, including curricula. Benefits result from this since it keeps the workplace climate acceptable.
As a result, the statement was true are the aforementioned. Therefore, option (a) is correct.
Learn more about on resume, here:
https://brainly.com/question/2964410
#SPJ4
A photograph is created by what
A) Silver
B) Shutters
C) Light
4) Mirror
Answers
A photograph is created by Light.
What are photographs made of?Any photograph created is one that is made up of Support and binders.
The steps that are needed in the creation of a photograph are:
First one need to expose or bring the film to light.Then develop or work on the imageLastly print the photograph.Hence, for a person to create a photograph, light is needed and as such, A photograph is created by Light.
Learn more about photograph from
https://brainly.com/question/25821700
#SPJ1
a fellow analyst believes that an attacker briefly authenticated to your company wifi network and might have compromised some machines. your colleague collected network traffic and ran two splunk queries that might be helpful in your investigation. attached are resources provided by the analyst for your evaluation. course hero
Answers
You can always choose to perform a Windows reinstall (clean install/reformat) instead, which would delete all dangerous files associated to ransomware and destroy all of your computer's data, including all of your files, installed programs, and settings, so make a backup of your crucial information first.
How to illustrate the information?It is malware that corrupts files and spreads when the infected file or another application runs it. The impact of hostile code can be innocuous or can result in the loss of data and resources.
Simply reinstalling the operating system won't be able to unlock your files because the ransomware (as it is typically understood) has encrypted all of your crucial documents, pictures, videos, and other types of files while typically leaving your operating system operational.
The best way to recover from a disk image backup is to simply restore the disk image, overwriting any existing data to get back what you had before the backup.
Therefore, you can fully re-install Windows on the victim machine by destroy all of your computer's data, as reinstalling.
Learn more about Window on:
https://brainly.com/question/25243683
#SPJ1
A fellow analyst believes that an attacker briefly authenticated to your company wifi network and might have compromised some machines. your colleague collected network traffic and ran two splunk queries that might be helpful in your investigation. attached are resources provided by the analyst for your evaluation
Why should you fully re-install Windows on the victim machine?
What are three advantages of using desktop software on a desktop computer
rather than mobile software on a smartphone or tablet?
A. It is extremely portable and easy to transport.
B. Using a mouse allows more precision when selecting objects on
the screen.
C. It is easier to type in text quickly using a keyboard.
D. It offers more features, and the interface fits well on a bigger
screen.
Answers
Answer:
A. It offers more features, and the interface fits well on a bigger screen.
B. Using a mouse allows more precision when selecting objects on the screen.
C. It is easier to type in text quickly using a keyboard.
Studies have shown that is the most effective means to mobilize voters.
a. an email
b. a piece of direct mail
c. personal contact
d. a telephone call
Answers
Personal contact has been shown to be the most effective means to mobilize voters.
Studies have consistently found that face-to-face interactions, such as canvassing or door-to-door campaigning, have a significant impact on voter turnout. These personal contacts allow for direct communication, building trust, answering questions, and addressing concerns, which can be more persuasive and influential than other forms of communication. While other methods like email, direct mail, and telephone calls can still be effective in reaching voters and conveying information, they often lack the personal touch and direct interaction that personal contact provides.
Personal contact allows for a deeper level of engagement, enabling campaigners to establish a connection, understand individual concerns, and tailor their message accordingly. However, it's worth noting that the effectiveness of mobilization efforts can vary depending on the specific context, target audience, and campaign strategy. A combination of multiple communication methods, including personal contact, can be even more impactful in reaching and mobilizing a diverse range of voters.
Learn more about voter mobilization strategies here:
https://brainly.com/question/30647053
#SPJ11.
Preview how the results of this query will look when printed when the page orientation is changed to landscape.
Answers
When the page orientation is changed to landscape, the printed query results will be displayed horizontally across the page, providing more space for the columns and potentially fitting more data on a single page. This orientation is particularly useful when dealing with a large number of columns or wider content.
The landscape orientation typically results in the following changes:
1. Wider columns: Since the page is wider, columns in the query results can be adjusted to occupy more horizontal space, reducing the need for text wrapping and making the data easier to read.
2. More columns per page: The increased width allows for more columns to be displayed side-by-side on a single page, reducing the need for additional pages and making it easier to compare data across columns.
3. Improved readability: With more space for columns and reduced text wrapping, the overall readability of the printed query results can be improved.
4. Possible reduction in the number of pages: As landscape orientation allows for more data to be displayed on a single page, the total number of pages required to print the entire query results may be reduced.
In summary, changing the page orientation to landscape for printing query results can lead to wider columns, more columns per page, improved readability, and a possible reduction in the number of pages needed. However, the actual appearance will depend on the specific query results and the formatting settings applied when printing.
Learn more about orientation here:
https://brainly.com/question/12331456
#SPJ11
Question 2 of 10
You can only use the inspect element on a few webpages.
(1 point)
True
False
Answers
True because it depends
Calculate the voltage between two points of the circuit of an iron through which a current of 4 amps passes and presents a resistance of 10 ohms
Plz i need it
Answers
def voltage_calculation (i, r):
return i*r
Which distinct type of VLAN is used by an administrator to access and configure a switch?
data VLAN
default VLAN
native VLAN
management VLAN
Answers
A management VLAN is a distinct type of VLAN used by administrators to access and configure a switch. This separate VLAN allows for secure and efficient management of the network infrastructure.
A Management VLAN is a virtual Local Area Network (VLAN) that is used to manage and control network devices such as switches, routers, and servers. The purpose of the Management VLAN is to segregate management traffic from user traffic, providing an additional layer of security and simplifying network administration.
By using a separate VLAN for management traffic, network administrators can limit access to network devices to only authorized personnel. In addition, the Management VLAN can be used to prioritize management traffic over user traffic, ensuring that network administrators can access and manage devices even during periods of high network utilization. Some common uses of the Management VLAN include:
Remote device management: By using the Management VLAN, network administrators can remotely manage network devices from a central location, without needing physical access to the devices.
Network monitoring: The Management VLAN can be used to send network monitoring traffic to a central monitoring system, providing administrators with visibility into network performance and potential issues.
learn more about vlan:https://brainly.com/question/28635096
#SPJ11
So I got the MSI GE76 Raider and I dont know if I should get a new better gaming laptop or not, is the GE76 good for gaming?
Answers
Answer:
yes it is
Explanation:
The MSI GE76 Raider is one of the best gaming laptops for those looking for a desktop replacement. It even brings excess amounts of RGB lighting courtesy of a full light bar under the wrist rest. Of course, that all comes at a cost.
steffi needs to find the domain name of the webpage she is currently viewing. to do this, she needs to look at the address bar of the browser.. t/f
Answers
Answer:
True
Explanation:
The address bar contains the url of the site. The url is the internet address of a given resource and contains the domain name
For example, your question on brainly has the address:
https://brainly.com/question/30515734
Here brainly.com is the domain name
Which HTML tag is formatted correctly?
NEED ANSWER ASAP PLZ HELP ME IDONT UNDERETAND IT
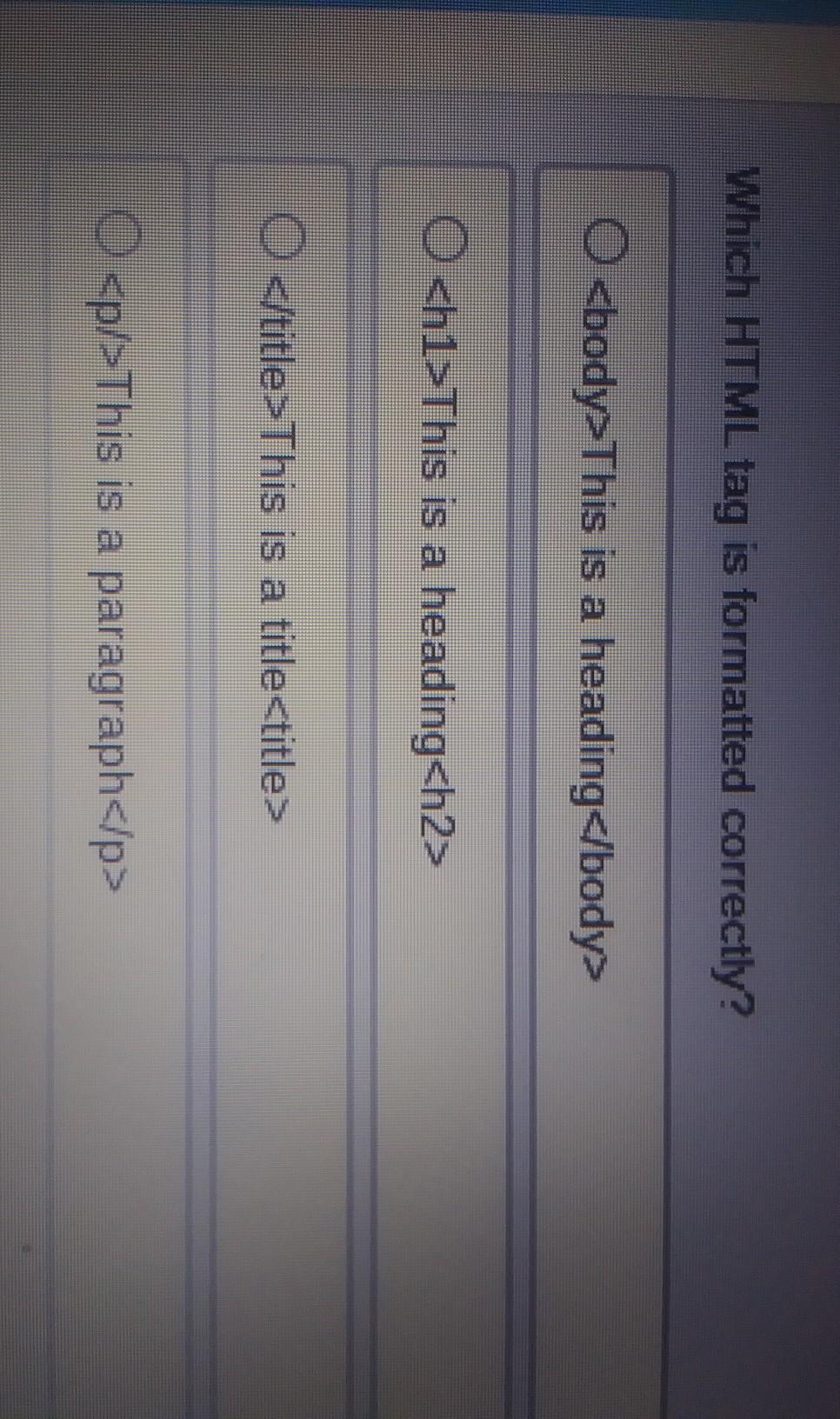
Answers
I think the last one is the correct one
Answer:
D
Explanation:
All others don't work
Select the correct answer.
Ben wants to keep similar items close to each other in the image he is working on. Which is the most effective technique for applying the gestalt
concept of proximity?
The BLANK technique is the most effective technique for applying the gestalt concept of proximity.
Answers
Gestalt Principles are principles/laws of human perception that describe how humans group similar elements, recognize patterns and simplify complex images when we perceive objects.
What are the Gestalt Principles?The tendency to view items as belonging to the same grouping when they are close to one another is known as the gestalt principle of
proximity
. It claims that regardless of how different the forms and sizes are from one another, if shapes are close to one another, you will perceive them as groups. One of Gestalt's principles, the concept of closeness focuses on how each stimulus would be seen in its most basic form. The
Law of Simplicity
or the Law of Pragnanz are other names for it. It is founded on the idea that the sum of a thing is worth more than the sum of its components.
To learn more about Gestalt Principles refers to;
https://brainly.com/question/4734596
#SPJ1
Step into my world
Bittersweet love story about a girl
Shook me to the core
Voice like an angel, I've never heard before
Here in front of me
Shining so much brighter than I have ever seen
Life can be so mean
But when he goes, I know he doesn't leave
[Pre-Chorus 1: Charlie Gillespie & Madison Reyes]
The truth is finally breaking through
Two worlds collide when I'm with you
Our voices rise and soar so high
We come to life when we're
[Chorus: Charlie Gillespie & Madison Reyes]
In perfect harmony
Woah, woah
Perfect harmony
Woah, woah
Perfect harmony
[Verse 2: Charlie Gillespie, Madison Reyes, Charlie Gillespie & Madison Reyes]
You set me free
You and me together is more than chemistry
Love me as I am
I'll hold your music here inside my hands
[Pre-Chorus 2: Charlie Gillespie & Madison Reyes]
We say we're friends, we play pretend
You're more to me, we're everything
Our voices rise and soar so high
We come to life when we're
[Chorus: Charlie Gillespie & Madison Reyes]
In perfect harmony
Woah, woah
Perfect harmony
Woah, woah
Perfect harmony
[Bridge: Charlie Gillespie, Madison Reyes, Charlie Gillespie & Madison Reyes]
I feel your rhythm in my heart, yeah-yeah
You are my brightest, burning star, woah-woah
I never knew a love so real (So real)
We're heaven on earth, melody and words
When we are together we're
[Chorus: Charlie Gillespie & Madison Reyes]
In perfect harmony
Woah, woah
Perfect harmony
Woah, woah
[Outro: Charlie Gillespie, Madison Reyes, Charlie Gillespie & Madison Reyes]
We say we're friends
We play pretend
You're more to me
We create a perfect harmony
Answers
Answer:
THIS SONG IS FIRE AND WHEN IT HAPPENED IN THE SHOW, I FAINTED*
Explanation:
Julie and the Phantoms is my favorite thing in the world.
What is the purpose of the Print Area feature?
Answers
A/an _____________ is a stored program that executes at a specified time. Group of answer choices stored procedure view trigger event
Answers
There are different kinds of program. A/an event is a stored program that executes at a specified time.
What is a Stored Program?This is known to be a program that is made up of one or plenty SQL statements that are saved in the database for future use.
The Four types of stored programs are:
Stored ProcedureStore FunctionTrigger EventConclusively, An Event is a program that is Executed at a scheduled or given time.
Learn more about program from
https://brainly.com/question/1538272
How did tribes profit most from cattle drives that passed through their land?
A.
by successfully collecting taxes from every drover who used their lands
B.
by buying cattle from ranchers to keep for themselves
C.
by selling cattle that would be taken to Texas ranches
D.
by leasing grazing land to ranchers and drovers from Texas
Answers
The way that the tribes profit most from cattle drives that passed through their land is option D. By leasing grazing land to ranchers and drovers from Texas.
How did Native Americans gain from the long cattle drives?When Oklahoma became a state in 1907, the reservation system there was essentially abolished. In Indian Territory, cattle were and are the dominant economic driver.
Tolls on moving livestock, exporting their own animals, and leasing their territory for grazing were all sources of income for the tribes.
There were several cattle drives between 1867 and 1893. Cattle drives were conducted to supply the demand for beef in the east and to provide the cattlemen with a means of livelihood after the Civil War when the great cities in the northeast lacked livestock.
Lastly, Abolishing Cattle Drives: Soon after the Civil War, it began, and after the railroads reached Texas, it came to an end.
Learn more about cattle drives from
https://brainly.com/question/16118067
#SPJ1
Teens are more likely to access the news online or by watching the news on TV.
OA. True
OB. False
Answers
The row's range of permissible values is known as its domain. True or False?
Answers
The given statement "The row's range of permissible values is known as its domain" is true because the permissible values called as domain.
In the context of mathematics and data analysis, a row is a horizontal sequence of values or observations in a table or matrix. The domain of a row refers to the range of permissible values that each element in the row can take. For example, consider a dataset that includes a row of measurements for the temperature of a particular location over the course of a year.
The domain of this row might be restricted to a certain range of values, such as -50 to 50 degrees Celsius, depending on the context of the data and the properties of the location being measured. The domain of a row can be specified by the researcher or analyst who is working with the data, or it may be determined by external factors such as physical constraints, measurement tools, or other contextual factors.
Learn more about domain: https://brainly.com/question/28934802
#SPJ11
(TOPIC: Video Games) For a bit of fun, What's you're *favorite* video game? And why?
Answers
Answer:
I love Breath of the Wild.
Explanation:
It is my favorite game of all time! Don't get mad at me, but I actually don't mind Zelda's English VA. It just has that tone of maturity in her voice that I really like. But I agree with all of you when I say that I wish that Patricia Summersett (Zelda's VA) did a better job with Zelda's cry in the Despair Cutscene (memory # 16). It just sounds like she is having a hard time breathing lol. But back to why I love the game: I LOVE THE SCENERY! IT IS ABSOLUTELY "BREATH"TAKING (haha see what I did there)! And also, Urbosa is queen. I wish she was in Smash instead of stoopid Piranha Plant.
Identify the key factors regarding the OpenAI's internal and
external situations and What are the
challenges and opportunities ahead for the company?
Answers
Internally, key factors include OpenAI's research and development capabilities, its technological advancements, and its organizational structure and culture. Externally, factors such as market competition, regulatory landscape, and customer demands shape OpenAI's situation.
The challenges ahead for OpenAI include addressing ethical concerns and ensuring responsible use of AI, maintaining a competitive edge in a rapidly evolving market, and addressing potential risks associated with AI technology. Additionally, OpenAI faces the challenge of balancing openness and accessibility with protecting its intellectual property and maintaining a sustainable business model.
However, these challenges also present opportunities for OpenAI, such as expanding into new industries and markets, forging strategic partnerships, and contributing to the development of AI governance frameworks to ensure the responsible and beneficial use of AI technology. OpenAI's continuous innovation and adaptation will play a crucial role in navigating these challenges and seizing the opportunities ahead.
To learn more about technology click here: brainly.com/question/9171028
#SPJ11
Help! I was doing my hw and I took a break and let my screen time out after like 10-15 minutes I turned it back on it showed this screen. I’ve broken so many things already and I have class tomorrow and all my stuff is on this computer I can’t I just can’t lose this computer so please help. I’ve tried powering it off, control-alt-and delete, and moving my mouse around but I can’t nothing pops up not even my curser so can all the computer smart people help me please I’m begging you!

Answers
Answer:
It looks like something got damaged or something with the operating system.
Explanation:
You should probably contact where you got the chromebook from and request a new one and have a tech at your school look into it. If its from school.
In which number system do the digital computer work
Answers
The numbers that are operated on by a digital computer is known as the binary number system; binary digits, or bits. These are 0's and 1's.
what is another name for a man-in-the-middle attack
Answers
Answer:
Close to you or with malware
Explanation:
there i beleive
Define a enumerated type Direction to make the following code work correctly. It should associate EAST with the value 0, NORTH with the value 90, WEST with 180 and SOUTH with 270.Code:#include using namespace std;//Do not modify anything on or above the line below this//YOUR_CODE_BELOW//YOUR_CODE//YOUR_CODE_ABOVE//Do not modify anything on or below the line above thisint main(){ int d1; cin >> d1; //map values over 360 and greater back into 0-359 range d1 %= 360; if(d1 == NORTH) { cout << "North" << endl; } else if(d1 == SOUTH) { cout << "South" << endl; } else if(d1 == EAST) { cout << "East" << endl; } else if(d1 == WEST) { cout << "West" << endl; } else { cout << "Error" << endl; }}
Answers
To make the provided code work correctly, we need to define an enumerated type 'Direction' which will associate the directions EAST, NORTH, WEST, and SOUTH with values 0, 90, 180, and 270, respectively. Here is how the solution will look like:
```#include using namespace std;
// Do not modify anything on or above the line below thisenum Direction
{
EAST, NORTH = 90, WEST = 180, SOUTH = 270
};
// Do not modify anything on or below the line above this
int main()
{
int d1;
cin >> d1;
// map values over 360 and greater back into 0-359 range d1 %= 360;
if(d1 == NORTH)
{
cout << "North" << endl;
}
else if(d1 == SOUTH)
{
cout << "South" << endl;
}
else if(d1 == EAST)
{
cout << "East" << endl;
}
else if(d1 == WEST)
{
cout << "West" << endl;
}
else
{
cout << "Error" << endl;
}
return 0;
}
```Note that we first declared an enumerated type "Direction" with four named constants EAST, NORTH, WEST, and SOUTH, each of which is associated with an integer value 0, 90, 180, and 270, respectively. Then, we used these named constants in the main function to compare with user input "d1" to check if it matches the predefined directions. If "d1" matches one of the predefined directions, we output the corresponding direction, otherwise we output "Error".
To learn more about enumerated type; https://brainly.com/question/14494958
#SPJ11
you are configuring a new system, and you want to use a raid 0 array for the operating system using sata disks and a special controller card that includes a raid processor. which raid method should you use?
Answers
Performance improvements are the key benefit of disk striping and RAID 0. For instance, three hard drives would offer three times the bandwidth of a single drive if data were striped over them.
Disk striping would enable up to 600 IOPS for data reads and writes if each drive operated at a rate of 200 input/output operations per second (IOPS). Disk striping is similarly used in RAID 5, however this version offers fault tolerance for a single disk failure. Disk striping divides data into smaller units and saves the units across a number of drives by simultaneously reading from and writing to each disk. Disk striping is used in RAID 0 but there is no fault tolerance. Hard disk drive (HDD) minimums and maximums for RAID 5 groups are both three.
Learn more about disk striping here-
https://brainly.com/question/14018617
#SPJ4
which of these describe raw data?check all of the boxes that apply A) what a person buys B) where a person lives C) data that has been analyzed D) data that has not been analyzed
Answers
What is the output of the following code:
lang=
['Python','C','C++, JAVA,ASP'PHP',VB', Oracle
'MySQL)
list1 = lang(2:-2]
list2 = langl-2:-5)
list3 = langl: : 3]
print(list)
print(list)
print(list3)
Answers
Answer:
Syntax error.
Explanation:
There are many typing mistakes in this source code.
what is the location of an ios backup stored on a local windows computer via itunes?
Answers
backups stored on a local Windows computer via iTunes are typically located in a specific folder in the user's AppData directory.
When you create a backup of an iOS device using iTunes on a Windows computer, the backup files are saved in a folder called "MobileSync." This folder is usually located within the user's AppData directory. The exact path to the backup location is as follows: "C:\Users<username>\AppData\Roaming\Apple Computer\MobileSync\Backup." Within the "Backup" folder, each iOS device's backup is stored in a separate folder with a unique alphanumeric name. These backup folders contain the encrypted backup files, including app data, settings, photos, messages, and other user data associated with the iOS device.
Learn more about iOS here:
https://brainly.com/question/31930499
#SPJ11